
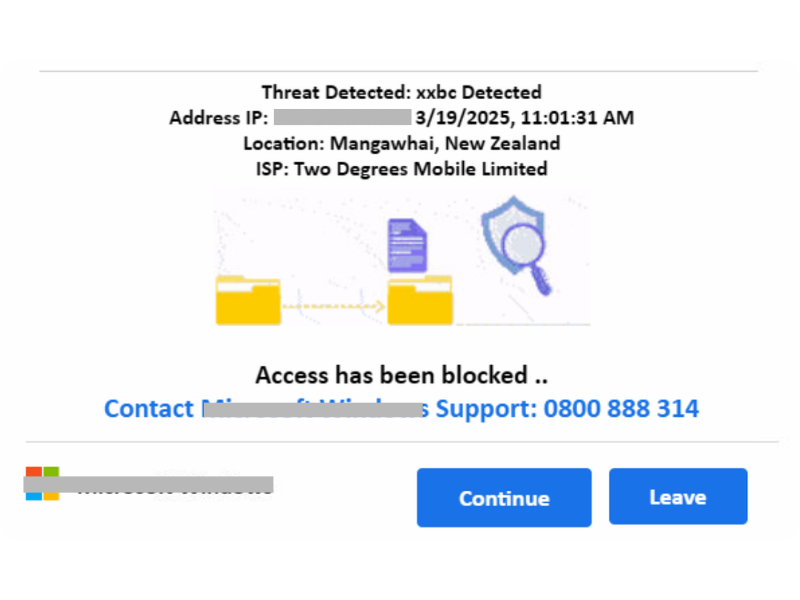
Unauthorised access scams involve attackers gaining access to your accounts, devices, or systems without permission. Often, through stolen credentials, phishing, or malware – in order to steal data, commit fraud, or carry out further attacks.
Unauthorised access scams are constantly evolving – this is just some of the common forms they can take.
Tips to avoid Unauthorised Access scams
Be wary of remote access requests – Legitimate organisations do sometimes use remote software tools for convenience to assist in resolving issues; however, look out for the following red flags:
If you suspect that the remote access is illegitimate, or something you have just done might have been an Unauthorised access scam, follow these steps:
Reach out to us, our local experts are here to help.